Automating KYC/KYB Verification Across Government and Sanctions Databases (March 2026)

Your compliance team burns hours logging into government portals one at a time because the KYC verification automation you built six months ago broke when OFAC updated their search interface. This happens constantly. Secretary of State registries redesign their pages, sanctions databases add new form fields, and suddenly you're back to manual checking across 50 states. What you need is automation that adapts to interface changes without custom code updates every few weeks. The shift is already underway: 85% of organizations are already integrating AI agents in at least one workflow. Yet most of these workflows still hit a wall when they encounter the browser, the one interface where APIs don't exist and traditional automation breaks.
TLDR:
- Manual KYC checks cost $13-$130 each; banks spend $60M annually on verification processes
- Automated verification queries OFAC, state registries, and sanctions databases simultaneously
- Skyvern interacts with government portals visually, adapting to UI changes without maintenance
- Each verification generates timestamped audit trails proving regulatory due diligence
- Skyvern automates browser-based KYC workflows using LLMs, handling CAPTCHAs and MFA across portals
Why KYC/KYB Verification Automation Matters in 2026
Financial services companies are spending money on a problem that shouldn't exist anymore. Manual KYC and KYB verification ties up teams in repetitive portal work, checking government databases and sanctions lists one search at a time. The costs add up fast. Manual verification checks cost between $13 and $130 per individual check. For banks, KYC processes cost $60 million annually on average, with individual checks ranging from $10 to $100. That's before counting the opportunity cost of compliance teams stuck doing work that could run automatically.
The manual approach creates other problems beyond cost. Verification times stretch to days or weeks, slowing customer onboarding and deal cycles. Human error rates increase with volume. Audit trails depend on someone remembering to document each step. When regulators ask for proof of due diligence, teams scramble to reconstruct what happened weeks ago.
In 2026, the gap between what compliance teams need to verify and what they can verify manually keeps widening. More jurisdictions require sanctions screening. Beneficial ownership rules expand. Customer expectations for fast onboarding rise. Hiring more people to log into more portals isn't a scalable answer.
Most enterprises see 60-80% cost savings switching from traditional automation to AI-powered platforms, with median payback periods under 12 months. Organizations implementing AI-powered automation report an average ROI of 171%, with enterprises achieving up to 70% cost reduction through workflow automation. The broader trend is even more compelling: no-code automation projects yield 2560% average ROI. This economic advantage stems from eliminating the ongoing maintenance burden that makes traditional automation unsustainable at scale, where teams spend more time fixing broken selectors than they save from the automation itself. Most teams can deploy their first automated workflow in 2-3 hours. Complex multi-step processes like policy renewals or compliance reporting take 1-2 weeks to fully optimize and test across all systems.
Automation closes that gap. The question isn't whether to automate KYC and KYB verification anymore. It's how to do it without building brittle scripts that break every time a government portal updates its UI.
How Government Database Verification Works

Government KYC and KYB verification pulls from multiple official databases that don't communicate with each other. Each requires its own search interface, login flow, and data format.
Business verification starts with Secretary of State registries, which hold entity formation documents, registered agent information, and active status across all 50 states using government form automation. State business registries maintain licensing data, tax registrations, and ownership records. International commercial registers like Companies House in the UK or Handelsregister in Germany provide formation and director information for foreign entities. Sanctions screening involves checking the OFAC SDN list, Consolidated Sanctions List, and BIS Entity List for export control restrictions. State-level professional licensing boards verify credentials for licensed industries.
Manual verification means logging into each database separately, searching one name at a time, and repeating the process across every required jurisdiction. Automation capabilities run all searches simultaneously. Automation, though, runs all searches simultaneously. Submit a business name and jurisdiction list once, and the system queries all relevant registries, returns structured results in minutes, and completes in hours what previously took days.
AI-powered web scraping delivers 30-40% faster data extraction times and achieves accuracy rates of up to 99.5% when handling dynamic, JavaScript-heavy websites compared to traditional methods. This performance gain stems from visual understanding that bypasses the complexity of parsing dynamic DOM structures, allowing Skyvern to extract data as efficiently as a human would read it.
The Hidden Costs of Manual KYC/KYB Processes
The per-check cost is just the starting point. The real damage happens at scale.
A single corporate client KYC review takes 31 to 60 days for 40% of banks to complete. During that window, deals stall, customers shop competitors, and revenue sits in limbo. Banks responding to this bottleneck throw headcount at the problem: most run teams of 1,001 to 2,000 full-time employees just managing KYC operations, with the largest firms running teams of 3,000 FTEs. That headcount doesn't scale with volume. When verification requests spike, backlogs grow. When portals change their UI or go down, teams work around it manually, often making mistakes that create risk. When auditors request documentation, staff reconstruct verification steps from memory and scattered screenshots.
Customer friction compounds the problem. Onboarding delays send high-value prospects elsewhere. Periodic re-verification interrupts existing relationships. Every manual touchpoint introduces error risk and extends timelines.
These aren't problems you solve with better training. They're structural issues that require different infrastructure. Automation isn't an add-on. It's what makes compliance work at the speed business actually moves.
Verification Aspect | Manual Process | Automated Process |
|---|---|---|
Cost per check | $13-$130 per individual | Fraction of manual cost at scale |
Corporate KYC timeline | 31-60 days (40% of banks) | Minutes to hours |
Team size required | 1,001-3,000 FTEs for large banks | Minimal staff for review/decision-making |
Database queries | Sequential, one at a time | Parallel across all registries |
UI change handling | Manual workarounds, errors increase | Adapts automatically without maintenance |
Audit trail creation | Manual screenshots, incomplete records | Automatic timestamped documentation |
OFAC list updates | Weekly/monthly checks create gaps | Real-time screening against current lists |
Scalability | Requires proportional headcount growth | Handles volume spikes without scaling staff |
Sanctions Screening and OFAC Compliance Requirements
OFAC screening is mandatory for financial institutions, money services businesses, and any company handling cross-border transactions that must handle authentication across multiple portals. These organizations must verify customers and counterparties against U.S. sanctions lists before onboarding and throughout the relationship lifecycle.
The requirement covers three primary lists:
- The Specially Designated Nationals list identifies individuals and entities blocked from accessing the U.S. financial system.
- The Foreign Sanctions Evaders list targets parties evading sanctions through evasion schemes.
- The Consolidated Sanctions List aggregates multiple programs into a single searchable database.
OFAC updates these lists frequently, sometimes multiple times per week. Companies must screen existing customers and transactions against the latest versions continuously. A customer cleared last month could appear on the SDN list today, creating compliance exposure. This is why manual screening isn't a scalable solution. It simply can't keep pace with this update frequency. Teams checking lists weekly or monthly create exposure windows where sanctioned parties slip through undetected. Downloading PDF lists and running manual name matches introduces false positives that consume investigation time.
Automated screening runs checks against current list versions in real time. When OFAC publishes updates, systems re-screen the entire customer base automatically. New onboarding applicants get checked against live data before approval, and the system flags matches instantly with timestamped records proving due diligence for examiners. Human review remains necessary for investigating matches and making final decisions.
Cross-Checking Multiple Government Data Sources
Business verification requires cross-referencing fragmented records across systems that were never built to work together.
For example, a complete KYB check pulls data from state business registries in every jurisdiction where an entity operates, federal tax databases, professional licensing boards for licensed industries, and international commercial registers for foreign ownership structures. Each system uses different search parameters, date formats, and entity name conventions. Delaware might list an entity as "Example Corp" while California shows "Example Corporation" and federal records use the EIN-linked legal name. Manual verification means running each search individually, waiting for results, comparing discrepancies, and deciding whether "John Smith" at one location matches "J. Smith" at another. A single entity verification takes hours.
Automation queries all databases in parallel. Submit one entity name and jurisdiction list, and the system runs simultaneous searches across every required registry. Results return in structured JSON with normalized entity names, locations, and status fields. Discrepancies get flagged for review instead of surfacing weeks later during an audit.
When verification scope includes 100 entities across multiple countries, manual checking becomes unworkable. Automated orchestration handles it without scaling headcount.
Building Audit Trails for Regulatory Compliance
Regulators require timestamped records showing what you searched, when you searched it, what results you found, and who reviewed the findings.
Manual verification creates documentation gaps. Compliance staff perform searches, take screenshots occasionally, and log results in spreadsheets or ticket systems. When an examiner asks for proof that you screened a specific entity against current sanctions lists, teams reconstruct what probably happened from incomplete records. Automated verification, on the other hand, generates complete audit trails by default. Every database query gets logged with the exact timestamp, search parameters used, data source version queried, and full results returned. If OFAC updates its SDN list and you re-screen your customer base, the system captures evidence of every check performed. When this process is automated, examiners request documentation and you can produce structured reports showing verification history for any entity or time period. The system proves that checks occurred and that they used current data sources and followed consistent procedures.
Automated audit trails free your team from documentation work so they can focus on investigating flagged matches and making risk decisions.
Different Approaches to KYC Automation
Several categories of tools tackle parts of the KYC automation problem, each with specific tradeoffs that affect their fit for multi-portal verification workflows.
Infrastructure-Focused Platforms
Airtop, Browserbase, and Hyperbrowser AI provide managed cloud browser infrastructure that eliminates the burden of maintaining browser fleets. These platforms handle browser provisioning, session management, proxy rotation, and fingerprint randomization, allowing developers to focus on automation logic instead of infrastructure concerns.
The limitation for KYC workflows appears when websites change. These platforms still require developers to write and maintain automation scripts using traditional selectors (CSS, XPath) that break when government portals update their UI. A Secretary of State registry redesign means updating every script that touches that portal. When you're verifying across 50 state registries and multiple sanctions databases, selector maintenance becomes a full-time job. In addition, none of these platforms include native 2FA or CAPTCHA solving capabilities that KYC portals frequently require, forcing teams to integrate third-party services separately. Teams using infrastructure platforms still face the core maintenance problem: someone needs to fix the scripts every time a portal changes.
Hybrid Tools
Stagehand takes a different approach by wrapping Playwright with AI-assisted actions. The tool lets developers write TypeScript code that mixes traditional programmatic control with natural language commands for simple interactions. This hybrid model appeals to teams that want some AI assistance without fully committing to a pure AI approach.
The maintenance burden persists. While AI assistance reduces the frequency of updates, Stagehand workflows still depend on site-specific code and selectors that break when websites change their structure. The framework provides AI help for individual actions but not end-to-end workflow intelligence that adapts to UI changes automatically. For KYC workflows spanning dozens of different portals, teams still write and maintain separate code for each site. When a portal redesigns its search interface, developers need to update the code. The hybrid approach reduces but doesn't eliminate the maintenance overhead that makes traditional automation unsustainable at scale.
No-Code Platforms
Browse AI and Director market themselves as accessible alternatives that let non-technical users create automations through point-and-click interfaces or natural language prompts. Browse AI trains "robots" for specific websites through visual recording. Director uses AI to translate natural language into browser actions.
Both hit the same wall when websites change. Browse AI robots break when target sites update their layout, requiring manual retraining. Director's AI-assisted workflow creation doesn't provide runtime adaptability to handle website changes dynamically. Once a workflow is created, it remains static and brittle. For KYC verification, the per-site configuration requirement becomes unworkable. Browse AI requires a separate robot for each portal, meaning an insurance agency working with 40 carrier portals needs 40 individual robots, each requiring maintenance when its target site changes. Director workflows break when government registries update their UI, forcing users back into the builder to fix and redeploy. Neither platform includes native authentication handling for 2FA or MFA flows that dominate enterprise KYC portals.
Data Extraction Tools
Firecrawl positions itself as an API-first web scraping tool that converts websites into clean, structured data for LLM consumption. The platform excels at read-only data extraction tasks where teams need to pull content from websites for analysis or aggregation.
The limitation for KYC workflows is fundamental: Firecrawl is focused solely on data extraction instead of workflow automation. It cannot handle interactive browser actions like form filling, button clicks, or navigation through multi-step processes. KYC verification requires logging into OFAC portals, submitting search queries, downloading confirmation documents, and progressing through conditional logic based on search results. Firecrawl offers no native 2FA or CAPTCHA solving for the login-gated portals that hold verification data. It's limited to read-only operations without the ability to manipulate web pages or execute the interactive workflows that define KYC automation. Teams using Firecrawl for KYC would still need separate tools to handle authentication, form submission, and file downloads.
Automating KYC/KYB Verification Workflows with Skyvern
Skyvern handles KYC and KYB verification by interacting with government portals the way a compliance analyst would, running searches across multiple databases at once without breaking when interfaces update.
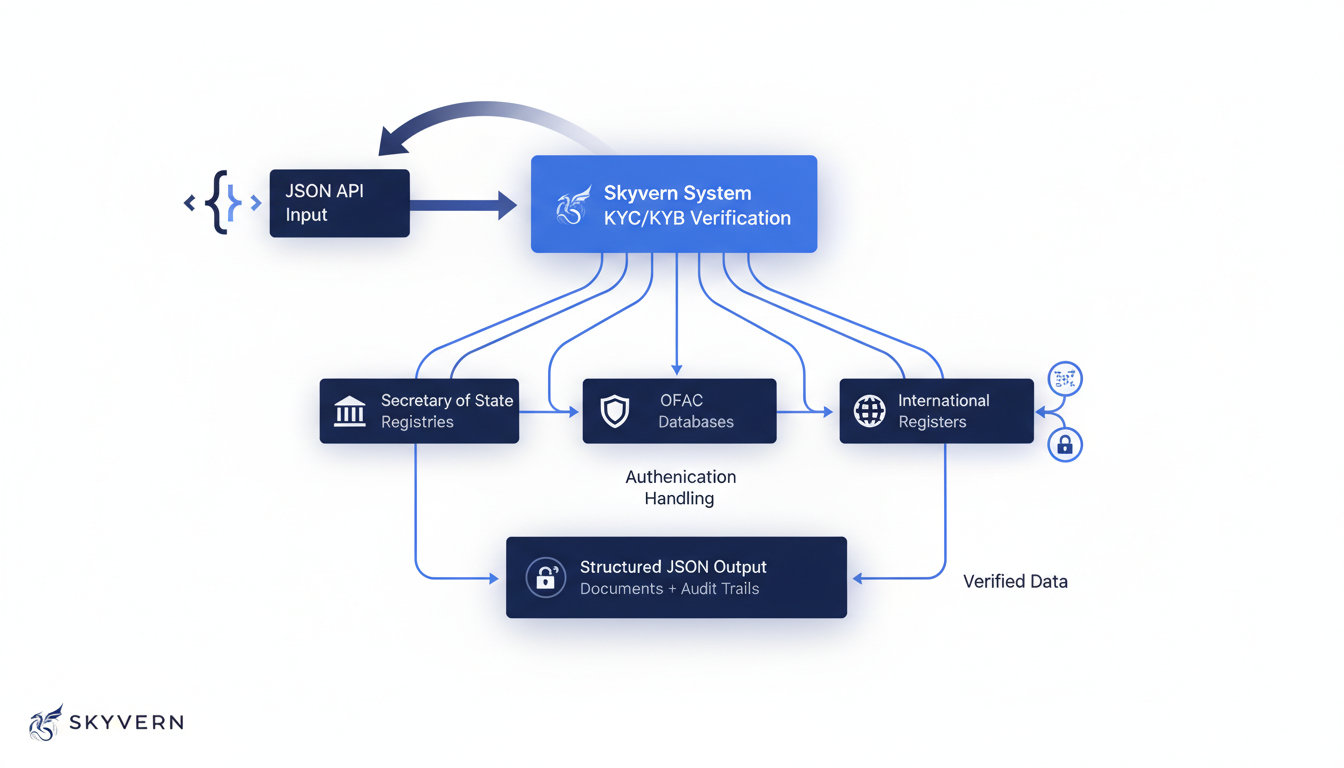
You send entity details as JSON through the API. Skyvern logs into each required portal, whether that's Secretary of State registries, OFAC databases, or international commercial registers. It handles CAPTCHA challenges, multi-factor authentication, and session timeouts while executing searches in parallel.
Skyvern reads portal interfaces visually instead of relying on CSS selectors or XPaths. When a state registry redesigns its search page, your workflow continues running without maintenance. When a sanctions database adds new form fields, Skyvern adapts without custom code.
The system works on day one and keeps working as your targets change. Unlike traditional automation that requires site-specific setup and breaks with every UI update, Skyvern operates immediately on any website (including ones it's never seen before) and continues to function reliably as websites evolve. This is the core competitive advantage: immediate functionality without configuration, and continued reliability without maintenance.
Results return as structured JSON via webhook, including downloaded confirmation documents and screenshot records of every step. Each verification generates an audit trail showing what was searched, when, and what data sources returned.
Developers can interact with Skyvern programmatically through the Python SDK. Initialize a client with Skyvern() and use methods like client.run_task() to automate browser workflows. The run_task method accepts parameters including url, navigation_goal, navigation_payload, data_extraction_goal, and extraction_schema, and returns a task object with properties like task.status and task.extracted_data for easy integration into Python applications.
The same workflow runs across all 50 states and international registries without building separate integrations for each jurisdiction.
Final Thoughts on Compliance Automation
You can't hire your way out of verification backlogs when government databases update weekly and customer expectations demand instant onboarding. KYC verification automation handles the repetitive portal work so your compliance team focuses on investigating matches and making risk decisions. Your current manual processes already cost more than automation, they just hide the expense in opportunity costs and bottlenecks. The infrastructure to verify at scale exists now.
FAQ
How long does automated KYC verification take compared to manual processes?
Automated KYC/KYB verification returns structured results in minutes instead of the 31 to 60 days that 40% of banks need for manual corporate client reviews. Parallel database queries run simultaneously across all required registries, completing in hours what previously took days of sequential manual searches.
What databases does Skyvern check during business verification?
Skyvern queries Secretary of State registries across all 50 states, OFAC sanctions lists (SDN, Consolidated Sanctions List, BIS Entity List), state-level professional licensing boards, and international commercial registers like Companies House. All searches run in parallel from a single API call, returning normalized results in structured JSON.
Does automated verification replace human compliance review?
No. Automation handles the repetitive portal work of running searches, checking sanctions lists, and generating audit trails. Human compliance staff still review flagged matches, investigate discrepancies, and make final risk decisions. The difference is your team spends time on analysis instead of logging into portals.
How does Skyvern handle government portal changes without breaking?
Skyvern reads portal interfaces visually using LLMs instead of relying on CSS selectors or XPaths that break when UIs update. When a state registry redesigns its search page or adds new form fields, your verification workflows continue running without requiring maintenance or custom code changes.

